Does it have to be complicated? – No it can be very easy
I often find discussion on websites concerning how to network-share files on a Linux computer with a Windows computer. One of the first topics that come up is the installation, setup, and use of Samba–which can become a bit complicated for the new Linux user. Samba is a very flexible and powerful SMB/CIFS software stack that also provides Domain Controller, print sharing, and a multitude of other incredibly useful features for the Linux server. Fortunately, in most cases for desktop Linux, this approach is not necessary at all.
With many modern desktop distributions, such as recent and current versions of Linux Mint, a Windows style SMB fileshare is very easy to setup and use because they have a samba GUI setup component built into Nemo, the default file browser. You need not edit any samba configuration files to setup fileshares at your Linux host. You can easily, and within seconds, share any user directory below your /home directory using Nemo. These fileshares can be easily accessed from other host systems including Linux, OS X, and Windows. You can easily control exactly how you want the fileshares you define accessed.
How to quickly create a fileshare on Linux Mint that you can access
Start Nemo, the default file browser and navigate to a directory somewhere below your home that you want to share. Rt-Click the directory of choice and select Properties. Then take a close look at the “Sharing” tab. In this case I Right-Clicked on a directory I had titled “tutorial” and you can see that the default share name provided matches the name of the directory.
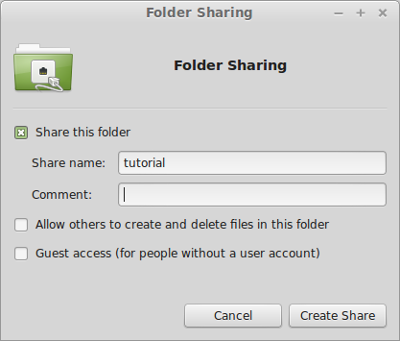
Select Share this Folder
This will let you access the folder from another system as a SMB share. Before you can actually access this you will need a samba password. So create one by going to the command line and typing
$ sudo smbpasswd -a user
...where user is your user name on the Linux system.
Now you can go to a Windows or OS X, or another Linux machine and access the share on your Linux system. Use the credentials of your Linux username and the smb password you provided when you ran the command above.
Samba passwords and Linux passwords are independent
Keep in mind that your Linux Mint password and your smb password are independent. They do not need to be the same and must be individually set. This means that you don’t have to use the same password to login to your Linux system as required to access your SMB shares on the Linux system.
You can always change your samba password on your Linux Mint system by going to the command prompt and simply entering:
$ smbpasswd
...prompts you for the old password then prompts twice for the new password
Other Methods of Setting up the Fileshare, Providing and/or restricting access to others
Going back to revisit the share Properties; you can select Guest access. This provides the share such that the user does not need to have an local or smb account to view the share as readonly. Anyone can then access the SMB share on the Linux box to read files. This presents a very open “Public” read-only type of share. Perhaps too open for some environments.
Revisiting the share Properties yet again, you could have instead selected Allow others to create and delete files in this folder. This will create the share such that the user must have an account on the Linux system, along with a smb user as well. This would allow the user read-write access to the share. In this example we must create both the new Linux user and new smb user associated with the Linux user.
$ sudo adduser shareuser
...adds new Linux user "shareuser" to the system and prompts twice for password entry
$ sudo smbpasswd -a shareuser
...adds shareuser as a smb user and prompts for password
Now shareuser can access the share you created. Guests with no local smb account entry will not have access at all. This type of share lets you share data with others who have the smb credentials you choose to provide them.
Of couse you can combine the settings, “Guest access” and/or “Allow others…” as desired to provide specific access to different users and/or groups of users.
Providing the writeable fileshare, while preventing user login access to my Linux system.
If you do not want the new user to be able to login to the Linux system, then you will have to be a bit more specific on exactly how the Linux account is created in the earlier example. You could instead create the user as follows:
$ sudo adduser shareuser --disabled-login
Creating the account this way will prevent the user from logging into the Linux system, but will allow them the required access to the fileshare. There are many other options for creating the user account. Refer to the man page for adduser for more details.
This simple, easy, and quick capability of sharing files should suit most use cases one might encounter for desktop/server filesharing. For those who need other capabilities and perhaps more flexibility in the filesharing approach, consider doing some additional research and resort to a manual samba server configuration.
